harley long (11 risultati)
Filtri di ricerca
Tipo di articolo
- Tutti i tipi di prodotto
- Libri (10)
- Riviste e Giornali (Nessun altro risultato corrispondente a questo perfezionamento)
- Fumetti (Nessun altro risultato corrispondente a questo perfezionamento)
- Spartiti (Nessun altro risultato corrispondente a questo perfezionamento)
- Arte, Stampe e Poster (Nessun altro risultato corrispondente a questo perfezionamento)
- Fotografie (Nessun altro risultato corrispondente a questo perfezionamento)
- Mappe (Nessun altro risultato corrispondente a questo perfezionamento)
- Manoscritti e Collezionismo cartaceo (1)
Condizioni Maggiori informazioni
- Nuovo (7)
- Come nuovo, Ottimo o Quasi ottimo (Nessun altro risultato corrispondente a questo perfezionamento)
- Molto buono o Buono (4)
- Discreto o Mediocre (Nessun altro risultato corrispondente a questo perfezionamento)
- Come descritto (Nessun altro risultato corrispondente a questo perfezionamento)
Legatura
- Tutte
- Rilegato (Nessun altro risultato corrispondente a questo perfezionamento)
- Brossura (10)
Ulteriori caratteristiche
- Prima ed. (Nessun altro risultato corrispondente a questo perfezionamento)
- Copia autograf. (Nessun altro risultato corrispondente a questo perfezionamento)
- Sovracoperta (Nessun altro risultato corrispondente a questo perfezionamento)
- Con foto (4)
- Non Print on Demand (10)
Lingua (2)
Prezzo
- Qualsiasi prezzo
- Inferiore a EUR 20 (Nessun altro risultato corrispondente a questo perfezionamento)
- EUR 20 a EUR 40
- Superiore a EUR 40
Spedizione gratuita
Paese del venditore
Valutazione venditore
-
OS X Exploits and Defense: Own it.Just Like Windows or Linux!
Da: Red's Corner LLC, Tucker, GA, U.S.A.
Paperback. Condizione: Good. Grade 2 out 5 points. This is a used book. Books has moderate wear on cover and pages. Books with this grade may have any of the following: Personalized notes/names, stickers/labels, markings on pages, bends/creases on cover/spine, ex-library markings. May not include extra materials such as dust jackets, access codes, CDs, accessories, etc. All orders ship by next business day! We are a small company and very thankful for your business!
-
paperback. Condizione: Good. Connecting readers with great books since 1972! Used textbooks may not include companion materials such as access codes, etc. May have some wear or writing/highlighting. We ship orders daily and Customer Service is our top priority!
-
Paperback. Condizione: Good. No Jacket. Pages can have notes/highlighting. Spine may show signs of wear. ~ ThriftBooks: Read More, Spend Less.
-
EUR 57,17
Spedizione EUR 7,52
Spedito da Regno Unito a U.S.A.Quantit�: 3 disponibili
Aggiungi al carrelloCondizione: New. pp. 354 Illus.
-
Condizione: New. pp. 354.
-
EUR 78,08
Spedizione gratuita
Spedito da Regno Unito a U.S.A.Quantit�: Pi� di 20 disponibili
Aggiungi al carrelloPaperback. Condizione: New. Contrary to popular belief, there has never been any shortage of Macintosh-related security issues. OS9 had issues that warranted attention. However, due to both ignorance and a lack of research, many of these issues never saw the light of day. No solid techniques were published for executing arbitrary code on OS9, and there are no notable legacy Macintosh exploits. Due to the combined lack of obvious vulnerabilities and accompanying exploits, Macintosh appeared to be a solid platform. Threats to Macintosh's OS X operating system are increasing in sophistication and number. Whether it is the exploitation of an increasing number of holes, use of rootkits for post-compromise concealment or disturbed denial of service, knowing why the system is vulnerable and understanding how to defend it is critical to computer security. Macintosh OS X Boot Process and Forensic Software All the power, all the tools, and all the geekery of Linux is present in Mac OS X. Shell scripts, X11 apps, processes, kernel extensions.it's a UNIX platform.Now, you can master the boot process, and Macintosh forensic software Look Back Before the Flood and Forward Through the 21st Century Threatscape Back in the day, a misunderstanding of Macintosh security was more or less industry-wide. Neither the administrators nor the attackers knew much about the platform. Learn from Kevin Finisterre how and why that has all changed! Malicious Macs: Malware and the Mac As OS X moves further from desktops, laptops, and servers into the world of consumer technology (iPhones, iPods, and so on), what are the implications for the further spread of malware and other security breaches? Find out from David Harley Malware Detection and the Mac Understand why the continuing insistence of vociferous Mac zealots that it "can't happen here" is likely to aid OS X exploitationg Mac OS X for Pen Testers With its BSD roots, super-slick graphical interface, and near-bulletproof reliability, Apple's Mac OS X provides a great platform for pen testing WarDriving and Wireless Penetration Testing with OS X Configure and utilize the KisMAC WLAN discovery tool to WarDrive. Next, use the information obtained during a WarDrive, to successfully penetrate a customer's wireless network Leopard and Tiger Evasion Follow Larry Hernandez through exploitation techniques, tricks, and features of both OS X Tiger and Leopard, using real-world scenarios for explaining and demonstrating the concepts behind them Encryption Technologies and OS X Apple has come a long way from the bleak days of OS9. THere is now a wide array of encryption choices within Mac OS X. Let Gareth Poreus show you what they are.
-
EUR 68,34
Spedizione EUR 9,95
Spedito da Germania a U.S.A.Quantit�: 3 disponibili
Aggiungi al carrelloCondizione: New. pp. 354.
-
OS X Exploits and Defense: Own it...Just Like Windows or Linux!
Da: Ria Christie Collections, Uxbridge, Regno Unito
EUR 68,93
Spedizione EUR 13,85
Spedito da Regno Unito a U.S.A.Quantit�: Pi� di 20 disponibili
Aggiungi al carrelloCondizione: New. In.
-
EUR 72,84
Spedizione EUR 75,17
Spedito da Regno Unito a U.S.A.Quantit�: Pi� di 20 disponibili
Aggiungi al carrelloPaperback. Condizione: New. Contrary to popular belief, there has never been any shortage of Macintosh-related security issues. OS9 had issues that warranted attention. However, due to both ignorance and a lack of research, many of these issues never saw the light of day. No solid techniques were published for executing arbitrary code on OS9, and there are no notable legacy Macintosh exploits. Due to the combined lack of obvious vulnerabilities and accompanying exploits, Macintosh appeared to be a solid platform. Threats to Macintosh's OS X operating system are increasing in sophistication and number. Whether it is the exploitation of an increasing number of holes, use of rootkits for post-compromise concealment or disturbed denial of service, knowing why the system is vulnerable and understanding how to defend it is critical to computer security. Macintosh OS X Boot Process and Forensic Software All the power, all the tools, and all the geekery of Linux is present in Mac OS X. Shell scripts, X11 apps, processes, kernel extensions.it's a UNIX platform.Now, you can master the boot process, and Macintosh forensic software Look Back Before the Flood and Forward Through the 21st Century Threatscape Back in the day, a misunderstanding of Macintosh security was more or less industry-wide. Neither the administrators nor the attackers knew much about the platform. Learn from Kevin Finisterre how and why that has all changed! Malicious Macs: Malware and the Mac As OS X moves further from desktops, laptops, and servers into the world of consumer technology (iPhones, iPods, and so on), what are the implications for the further spread of malware and other security breaches? Find out from David Harley Malware Detection and the Mac Understand why the continuing insistence of vociferous Mac zealots that it "can't happen here" is likely to aid OS X exploitationg Mac OS X for Pen Testers With its BSD roots, super-slick graphical interface, and near-bulletproof reliability, Apple's Mac OS X provides a great platform for pen testing WarDriving and Wireless Penetration Testing with OS X Configure and utilize the KisMAC WLAN discovery tool to WarDrive. Next, use the information obtained during a WarDrive, to successfully penetrate a customer's wireless network Leopard and Tiger Evasion Follow Larry Hernandez through exploitation techniques, tricks, and features of both OS X Tiger and Leopard, using real-world scenarios for explaining and demonstrating the concepts behind them Encryption Technologies and OS X Apple has come a long way from the bleak days of OS9. THere is now a wide array of encryption choices within Mac OS X. Let Gareth Poreus show you what they are.
-
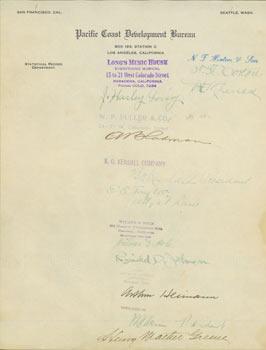
Autographs from noteworthy Californians on Pacific Coast Development Bureau letterhead. RE: Commercial Encyclopedia of the Pacific Southwest by Ellis A. Davis.
Editore: Los Angeles, CA: Pacific Coast Development Bureau, [1914]., 1914
Da: Wittenborn Art Books, San Francisco, CA, U.S.A.
Manoscritto / Collezionismo cartaceo
Condizione: Good. Letter-Sized Page, Signatures & Stamps on Pacific Coast Development Bureau Letterhead, Good with perforations, marginal tears, some toning & creasing. Provenance: Letters and Autographs from a Who's Who in California 1914 - 1917, to the author Ellis A. Davis, regarding Davis' Commercial Encyclopedia of the Pacific Southwest, California, Nevada, Utah, Arizona. Sold by Cherokee Book Shop to Frederick Ruffner, Jr., the founder of Gale Research, Detroit.
-
OS X EXPLOITS & DEFENSE
Da: moluna, Greven, Germania
EUR 51,08
Spedizione EUR 48,99
Spedito da Germania a U.S.A.Quantit�: Pi� di 20 disponibili
Aggiungi al carrelloKartoniert / Broschiert. Condizione: New. Dieser Artikel ist ein Print on Demand Artikel und wird nach Ihrer Bestellung fuer Sie gedruckt. Cuts through the hype with a serious discussion of the security vulnerabilities of the Mac OS X operating system Reveals techniques by which OS X can be owned Details procedures to defeat these techniques Offers a sober.